How it works
Neo manages on-premises Active Directory and Exchange Server by executing PowerShell scripts through your RMM platform. This enables the same operations available in cloud environments — password resets, user provisioning, group management, mailbox delegation, and more. Neo uses two execution patterns depending on your environment:- Direct execution — The RMM agent is installed on the target server (e.g., the Domain Controller or Exchange server). Neo runs scripts directly on it.
- Remote execution — The target server doesn’t have an RMM agent. Neo runs scripts on a “runner” VM that does have RMM, and uses PowerShell Remoting to reach the target server.
| Operation | Where it runs |
|---|---|
| AD changes (create user, reset password, groups, etc.) | On the AD Runner via RSAT — either the DC or a runner VM |
| AD Connect sync | On the AD Connect server (remotely from the runner if the AD Connect server isn’t in RMM) |
| Exchange Online / Exchange Hybrid standard ops (forwarding, delegation, shared mailbox, etc.) | Cloud — via Microsoft Graph |
Exchange on-prem cmdlets (e.g., Enable-RemoteMailbox) | On the Exchange server (remotely from the runner if the Exchange server isn’t in RMM) |
Setup
1. Configure Company Settings
For each client with on-prem infrastructure, configure their identity provider and mailbox provider settings in the Companies tab.Identity Provider Settings
| Field | Description |
|---|---|
| Identity Provider Type | Select “On-prem AD”, “Hybrid”, “Hybrid (no AD Connect sync)”, or “Entra ID (Cloud)“ |
| AD Runner Hostname | (On-prem AD and both Hybrid types) Hostname of the machine where AD scripts run — either the DC itself or a runner VM with RSAT AD tools. Must match the device name in RMM. |
| AD Service Account Username | (On-prem AD and both Hybrid types, optional) DOMAIN\username of the service account used for AD operations. |
| AD Connect Server Hostname | (Hybrid only) Hostname of the server running Azure AD Connect. Neo triggers a directory sync on this server after making AD changes, so updates propagate to Entra ID. If this server differs from the AD Runner, Neo uses remote execution to reach it. |
Which hybrid type? Choose “Hybrid” when Azure AD Connect syncs your on-prem AD to Entra ID — Neo makes identity changes in AD and triggers a sync so they propagate to the cloud. Choose “Hybrid (no AD Connect sync)” when both directories exist but nothing syncs between them (e.g., AD Connect was decommissioned) — Neo then performs every identity operation in both on-prem AD and Entra ID directly: user creation, password resets, sign-in blocking, deletion, and profile updates are applied to each side with the same values. Picking “Hybrid” without a working AD Connect leaves new users stranded in AD, never reaching the cloud.
Mailbox Provider Settings
| Field | Description |
|---|---|
| Mailbox Provider Type | Select “Exchange Server” (on-prem), “Exchange Hybrid”, or “Exchange Online” (cloud) |
| Exchange Server Hostname | (Exchange Server and Exchange Hybrid only) Hostname of the Exchange server |
| Exchange Runner Hostname | (Exchange Server and Exchange Hybrid, optional) Set this if the Exchange server doesn’t have an RMM agent. Neo runs scripts on this runner VM and uses remote execution to reach the Exchange server. Must match a device name in RMM. |
| Exchange Service Account Username | (Exchange Server and Exchange Hybrid, optional) DOMAIN\username of the service account. Required when using an Exchange Runner — enables CredSSP authentication to solve the Kerberos double-hop problem. |
Service Account Password
| Field | Description |
|---|---|
| Service Account Password | Password for the on-prem service account. Stored securely in Azure Key Vault — never stored in the database. Required when a service account username is configured. Leave blank when editing to keep the existing password unchanged. |
All hostnames must match exactly how the devices appear in your RMM platform.
2. Upload the Neo Script to Your RMM
Neo needs a wrapper script installed in your RMM to execute PowerShell commands.- ConnectWise Asio
- Datto RMM
- ConnectWise Automate
- NinjaOne
No upload required. ConnectWise Asio ships a built-in
PowerShell script automation template that Neo uses to execute PowerShell on managed endpoints. Neo dispatches the wrapper code inline as the body parameter of that template on every run, so you don’t need to create or maintain any Neo-specific script in your Asio library.Asio’s user-created PowerShell scripts (Add → PowerShell script in the Tasks page) don’t expose a “Parameters” tab, so Neo can’t use one as the wrapper. Don’t create a
[Neo Script] Run Powershell task in Asio — it won’t be used.- Confirm an Asio agent is installed on the target server (DC, Exchange server, runner VM, etc.) and reporting
osType=windows. - Trigger an RMM sync in Neo at Integrations → RMM so Neo discovers the endpoint and the built-in
PowerShell scripttemplate.
3. Set Up a Runner Machine
Required if: any server Neo manages (DC, Exchange server, AD Connect server) does not have an RMM agent installed. Common scenarios:
- You don’t want to install RMM on the Domain Controller
- The Exchange server doesn’t have an RMM agent
- The AD Connect server doesn’t have an RMM agent
3a. Install RSAT AD Tools
Required if: the DC doesn’t have an RMM agent (i.e., the runner performs AD operations on its behalf).
- Windows Server
- Windows 10/11
Open PowerShell as Administrator and run:Or via Server Manager: Add Roles and Features → Features → Remote Server Administration Tools → AD DS Tools → AD DS Snap-Ins and Command-Line Tools
Import-Module ActiveDirectory in PowerShell — it should complete without errors.
3b. Create a Dedicated Service Account
Create a service account in Active Directory (e.g.,DOMAIN\neo_automation) and grant it the permissions needed for the operations you want Neo to perform.
Active Directory permissions
Active Directory permissions
| Permission | Neo capabilities |
|---|---|
| Create/delete user objects | User onboarding and offboarding |
| Reset password | Password resets, unlock accounts, force password change at logon |
| Read/write all user properties | Update name, job title, department, manager, phone, office, company, employee ID, etc. |
| Enable/disable accounts | Enable/disable user accounts during onboarding/offboarding |
| Read/write group membership | Add/remove users from security and distribution groups |
| Read computer objects | View computer accounts and their properties |
| Enable/disable computer objects | Enable/disable computer accounts |
Exchange Server permissions (if using on-prem Exchange)
Exchange Server permissions (if using on-prem Exchange)
Assign the Recipient Management role to the service account, or delegate equivalent permissions:
If the Exchange server is not in RMM (i.e., Neo uses remote execution from a runner), the service account also needs WinRM remoting access to the Exchange server.
| Permission | Neo capabilities |
|---|---|
| Mailbox management | Convert user mailboxes to shared, delete mailboxes |
| Mail forwarding | Set up and remove email forwarding |
| Mailbox permissions | Grant/revoke Full Access to mailboxes |
| Recipient permissions | Grant/revoke Send As and Send on Behalf permissions |
| Address list visibility | Hide/unhide mailboxes from the Global Address List |
| Distribution group management | Create, delete, and manage distribution group membership |
| Mail contact management | Create and manage external mail contacts |
| Auto-reply configuration | Configure out-of-office messages |
| Mobile device management | View and wipe mobile devices (for offboarding) |
| Message tracking | Trace email delivery for troubleshooting |
| Transport rules | Create and manage mail flow rules |
| Public folder management | Create and manage public folders |
| Quarantine management | Release or delete quarantined messages |
| Inbox rules | View and manage user inbox rules |
| Calendar/resource management | Configure room and equipment booking policies |
| Retention policies | Configure message retention settings |
| Address list management | Manage GAL, OAB, and address book policies |
Azure AD Connect permissions (if using Hybrid identity)
Azure AD Connect permissions (if using Hybrid identity)
To trigger AD Connect syncs, the service account must be a member of the ADSyncOperators group on the AD Connect server.If the AD Connect server is not the same machine as the AD Runner (i.e., the AD Connect server is not in RMM), the service account also needs WinRM remoting access to the AD Connect server. Neo will use
Invoke-Command from the runner to trigger the sync remotely.Extended AD capabilities (optional)
Extended AD capabilities (optional)
Neo can also perform these Active Directory operations if you grant the necessary permissions:
| Permission | Neo capabilities |
|---|---|
| Create/delete computer objects | Computer account lifecycle management |
| Create/delete/modify OUs | Organizational unit management |
| Manage service accounts | Managed Service Account (MSA/gMSA) operations |
| Fine-grained password policies | View and modify password policies |
| Move/rename AD objects | Reorganize objects between OUs |
3c. Configure RMM Component Credentials
By default, Datto RMM scripts run under LocalSystem, which has no AD or Exchange permissions on non-DC machines. To run scripts under your service account, configure Component Credentials for each site that uses a runner machine.Component Credentials are configured per site (end-client). For sites without credentials configured, scripts run under LocalSystem — which only works if the RMM agent is installed directly on the DC or Exchange server.
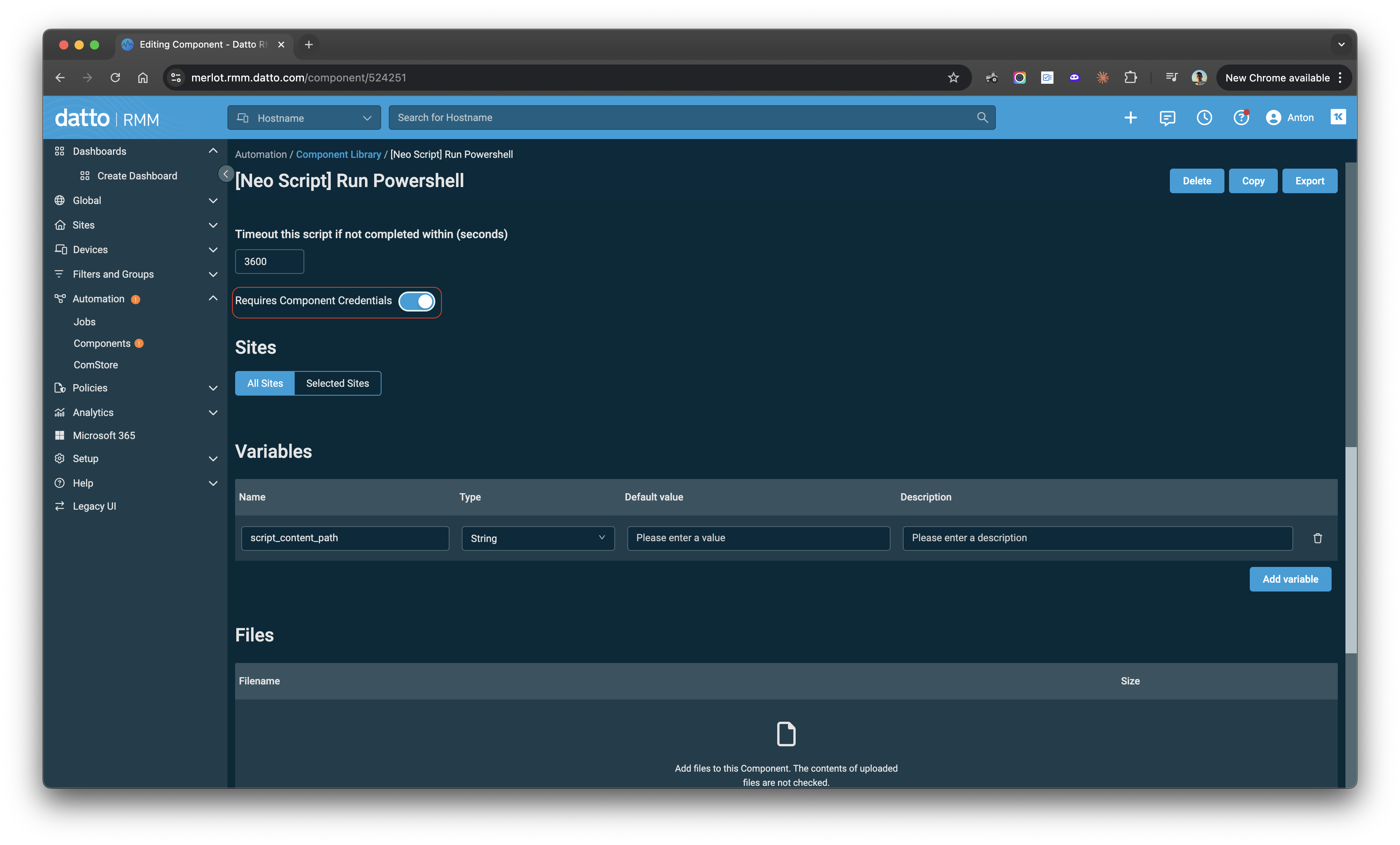
- Go to Automation → Components and open the [Neo Script] Run Powershell component
- Toggle Requires Component Credentials to ON
- Click Save to apply the change
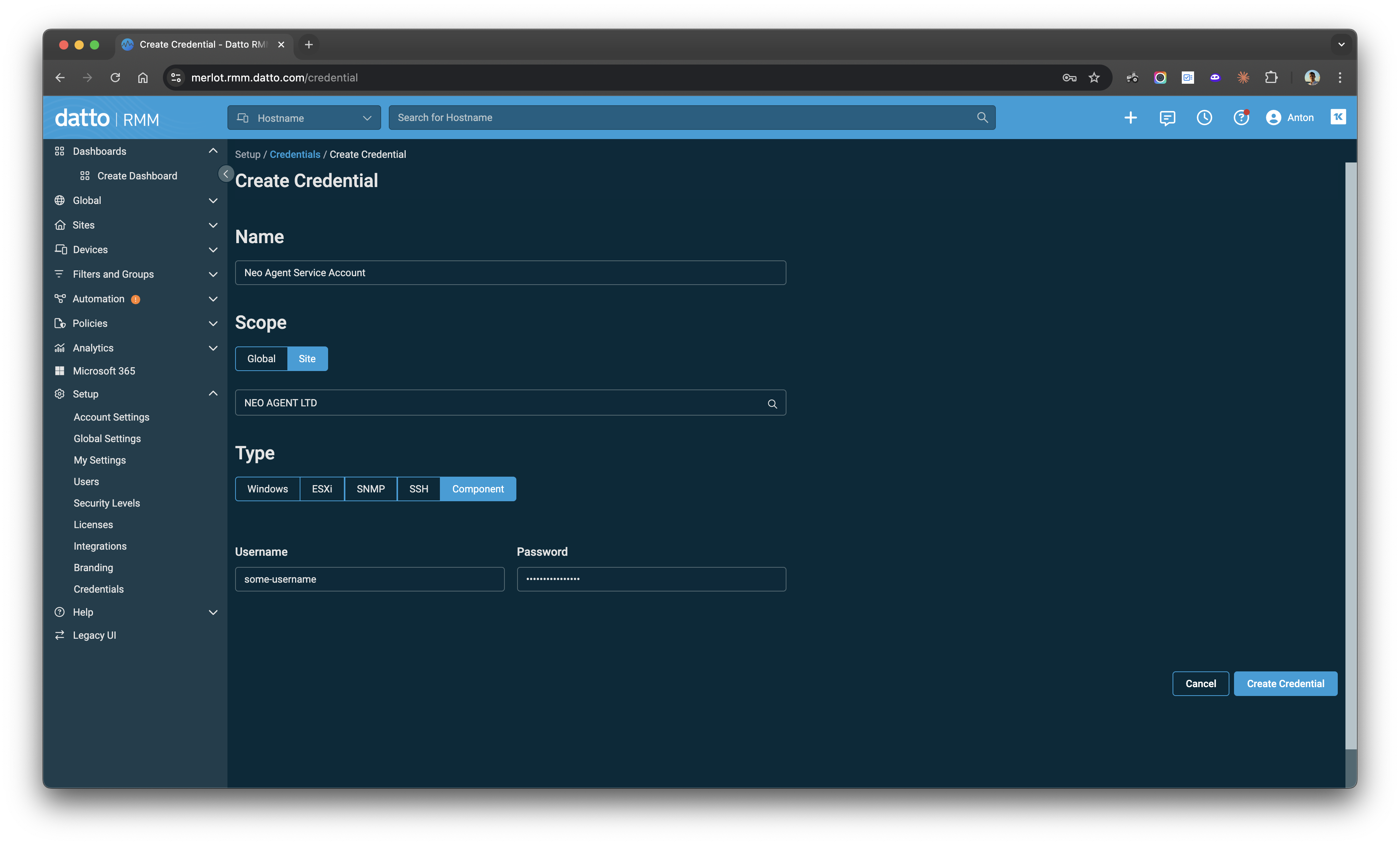
- In Datto RMM, go to Setup → Credentials → Create Credential
- Enter a Name (e.g., “Neo Agent Service Account”)
- Set Scope to Site and select the client’s site
- Set Type to Component
- Enter the service account credentials:
- Username:
DOMAIN\neo_ad_automation - Password: (the service account password)
- Username:
- Click Create Credential
4. Enable Remote Execution
Required if: a target server doesn’t have an RMM agent and Neo reaches it remotely from the runner. This applies when:
- The AD Connect server doesn’t have an RMM agent (AD Connect Server Hostname differs from AD Runner Hostname)
- The Exchange server doesn’t have an RMM agent (an Exchange Runner Hostname is configured)
-
Enable PowerShell Remoting:
This configures WinRM and opens the necessary firewall rules. See Microsoft’s documentation for details and troubleshooting.
- Grant the service account remoting access. The service account configured in Component Credentials must be able to establish remote PowerShell sessions to the target server. If the service account is not a Domain Admin, add it to the Remote Management Users group on the target server, or grant it WinRM access via Group Policy.
- Verify network connectivity from the runner to the target server on port 5985 (HTTP) or 5986 (HTTPS).
5. Configure CredSSP for Exchange Runners
Required if: the Exchange server doesn’t have an RMM agent and Neo reaches it remotely from the runner. This means:
- You configured an Exchange Runner Hostname in Mailbox Provider Settings
- The runner and Exchange server are different machines
- Exchange Service Account Username — e.g.,
CONTOSO\SVC_NEO_AUTOMATION - Service Account Password
EXCHANGE-SHORT with the Exchange server’s short hostname, EXCHANGE-FQDN with its FQDN, and *.yourdomain.com with your domain’s wildcard. Including all three forms prevents hostname resolution mismatches.
Step 3: Enable CredSSP on the Exchange server (server role).
On the Exchange server, open PowerShell as Administrator:
Get-ExchangeServer requires Exchange to query AD, so if it returns the server name, CredSSP is working end-to-end.
- If it succeeds — CredSSP is configured correctly.
- If it fails with “A computer policy does not allow the delegation of the user credentials” — re-run Step 2 with the correct hostname forms, including the wildcard.
- If it fails with a permissions error — CredSSP is working, but the service account may lack Exchange permissions.
6. Verify Connectivity
After completing setup, run these checks from the runner machine (or the DC if using direct execution) to confirm everything is working.Neo API connectivity
The machine running scripts must be able to reach the Neo API. Run:401 Unauthorized — this confirms the server can reach Neo over HTTPS. If you see an SSL error or timeout, see Troubleshooting.
AD tools (if using on-prem AD)
Verify the runner has the AD PowerShell module and can query the domain:Remote execution (if applicable)
If the AD Connect server or Exchange server is reached via remote execution, verify connectivity from the runner under the service account:- PowerShell Remoting is enabled on the target (
Enable-PSRemoting -Force) - The service account is in the Remote Management Users group on the target
- Port 5985 or 5986 is open between the runner and the target
Exchange Hybrid
Use Exchange Hybrid when a client has both on-prem Exchange and Exchange Online — typically during a migration or in long-term coexistence. How Neo routes operations:- Standard mailbox operations (forwarding, delegation, shared mailbox conversion, permissions, etc.) route to Exchange Online via Microsoft Graph — the same as pure Exchange Online clients.
- On-prem Exchange cmdlets (e.g.,
Enable-RemoteMailboxfor hybrid mailbox provisioning) are executed on the on-prem Exchange server when Neo’s agent determines they’re needed.
- Set Mailbox Provider Type to “Exchange Hybrid” in Company Settings
- Set the Exchange Server Hostname to the on-prem Exchange server
- (Optional) Set the Exchange Runner Hostname if the Exchange server doesn’t have an RMM agent — then complete Step 3, Step 4, and Step 5
Troubleshooting
”The supplied credential is invalid” on Exchange Runner
Symptom: Exchange operations (e.g.,Enable-RemoteMailbox) fail with:
- CredSSP client not configured: Run
Get-WSManCredSSPon the runner — it should show CredSSP is enabled as a client with the Exchange server in the delegate list. - CredSSP server not configured: Run
Get-WSManCredSSPon the Exchange server — it should show CredSSP is enabled as a server. - GPO blocking delegation: If you see “A computer policy does not allow the delegation of the user credentials”, re-run
Enable-WSManCredSSP -Role Clienton the runner with the FQDN, short hostname, AND domain wildcard forms. - Wrong password in Neo: Verify the service account password in the Companies tab is correct.
SSL/TLS Certificate Trust Error
Symptom: RMM scripts fail with an error like:engine.neoagent.io. This typically happens on older Windows servers with outdated root certificates.
Diagnose: Run this on the affected server:
- Expected result: 401 Unauthorized (confirms SSL/TLS is working)
- If you see an SSL error: The server’s certificate store needs updating
-
Update Windows root certificates — Install the latest Windows updates, or manually update certificates:
-
Check TLS 1.2 is enabled — Verify in registry:
- Check server clock — Certificate validation fails if the system time is significantly off
- Check for proxy/firewall interference — Some security appliances intercept HTTPS traffic and can break certificate chains
No Internet Access / Firewall Blocking
Symptom: RMM scripts fail with connection errors, timeouts, or “Unable to connect to the remote server.” Cause: The server running Neo scripts cannot reach the Neo API endpoint due to no internet access or firewall restrictions. Fix: Ensure the server can reachhttps://engine.neoagent.io. Add a firewall rule to allow outbound HTTPS (port 443) to this endpoint.
Diagnose: Run this on the affected server:
- Expected result: 401 Unauthorized (confirms connectivity is working)
- If you see a connection/timeout error: The server cannot reach the endpoint — check firewall rules and proxy settings
Other RMM Platforms
Neo supports on-prem execution through any RMM platform that can run PowerShell scripts, including:- N-Able N-Sight RMM
- N-Able N-Central
- ConnectWise RMM (Asio)
