Once you’ve created your OAuth Application Registry entry, you can connect ServiceNow to Neo Agent through the integrations dashboard.Documentation Index
Fetch the complete documentation index at: https://docs.neoagent.io/llms.txt
Use this file to discover all available pages before exploring further.
Unlike ConnectWise or Halo, ServiceNow uses an OAuth consent flow. After entering your credentials in the Neo dashboard, a popup window opens to your own ServiceNow instance where an admin approves access. The popup auto-closes when consent completes.
Required Information
Before starting the connection process, gather the following from the previous step:Your ServiceNow instance URL — for example
https://acme.service-now.com. Must use HTTPS, no trailing slash, no path. FedRAMP / Government Community Cloud customers can also use *.servicenowservices.com instances.The Client ID auto-generated when you saved your OAuth Application Registry entry.
The Client Secret from your OAuth Application Registry entry. Treat this like a password — Neo stores it encrypted in our Key Vault and uses it only to refresh access tokens.
Configuring the Integration
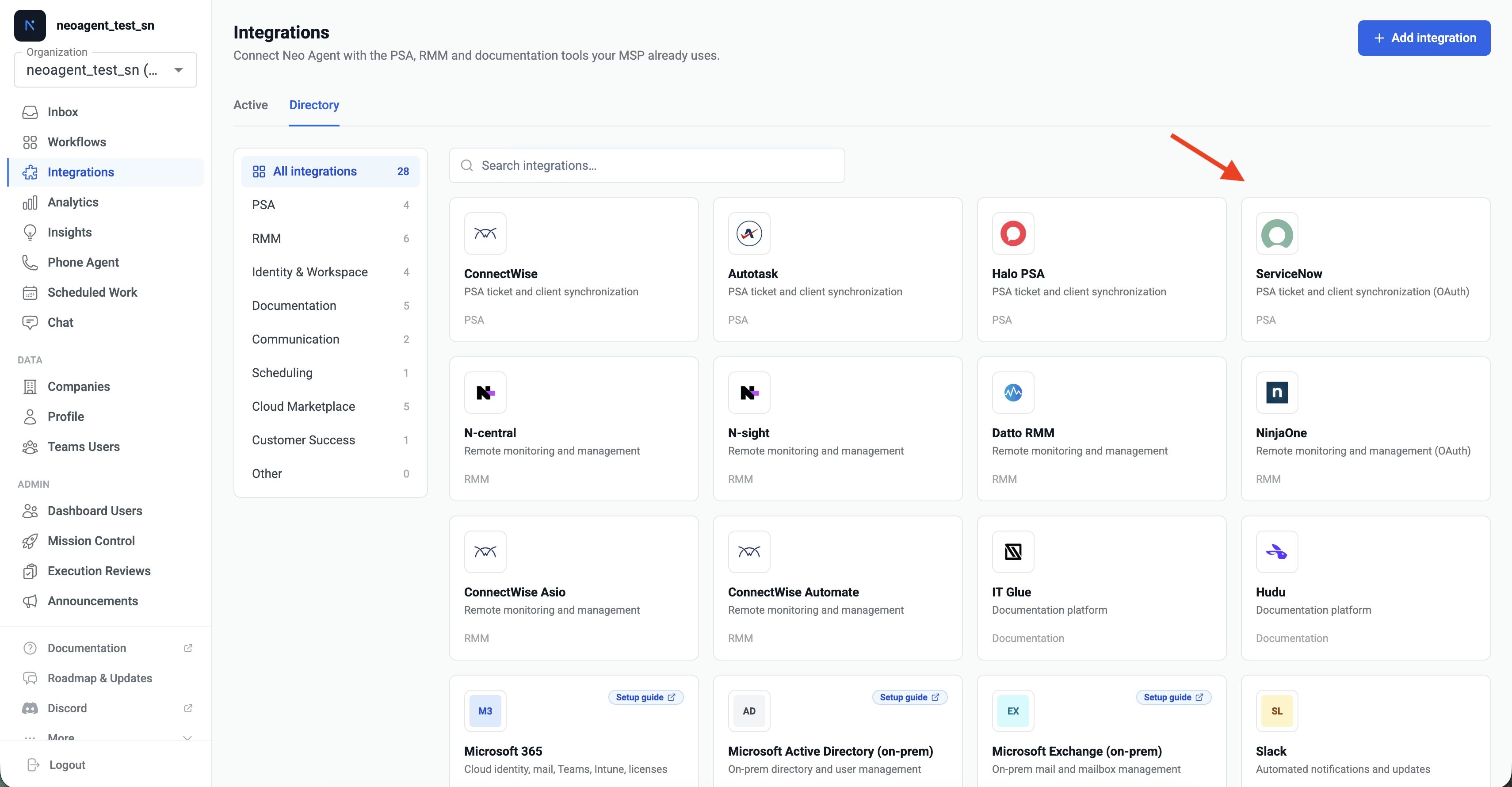
Open the Neo Agent dashboard and select ServiceNow
Navigate to the Neo Agent Dashboard, open the Directory tab, and click the ServiceNow tile.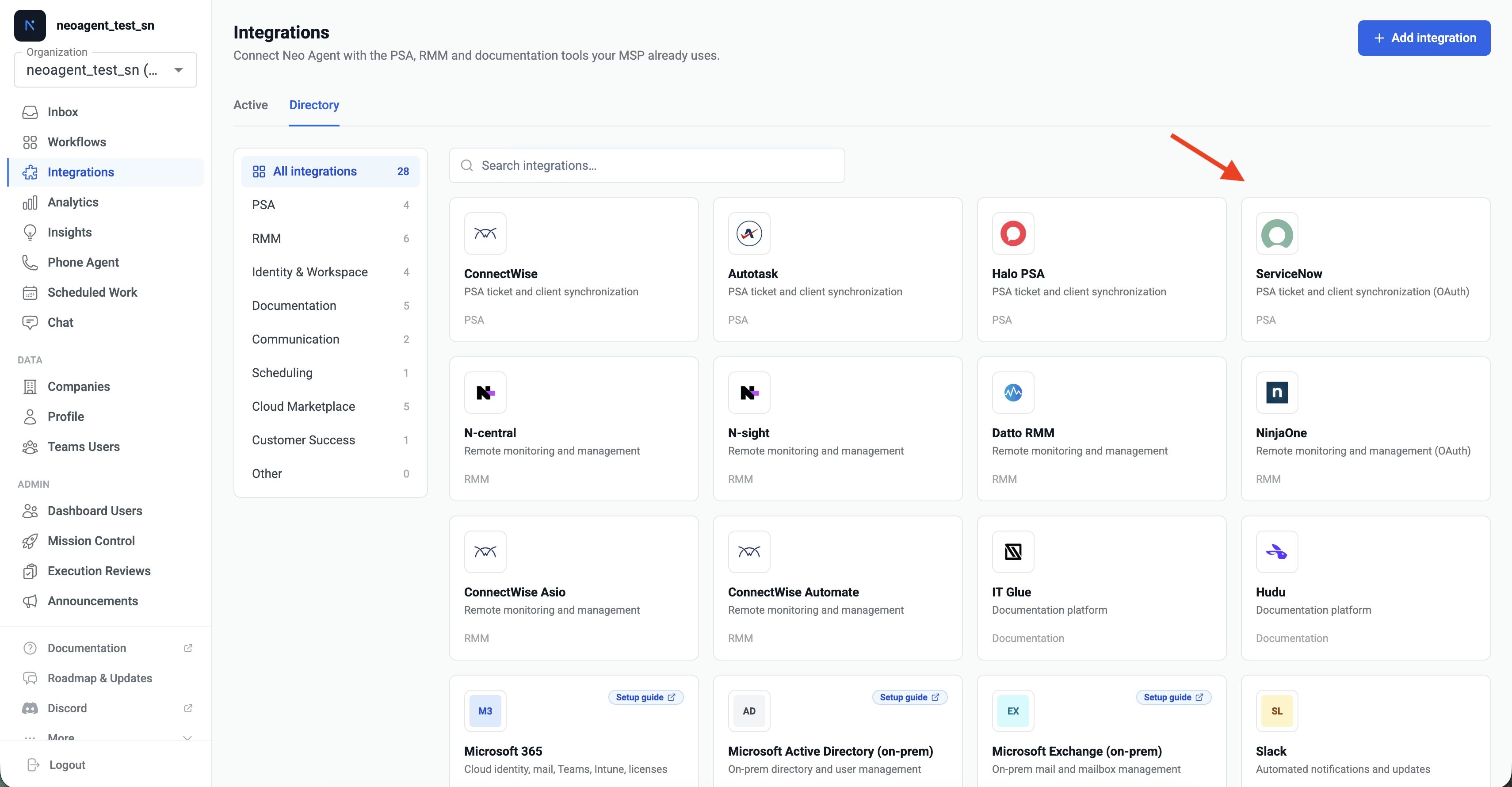
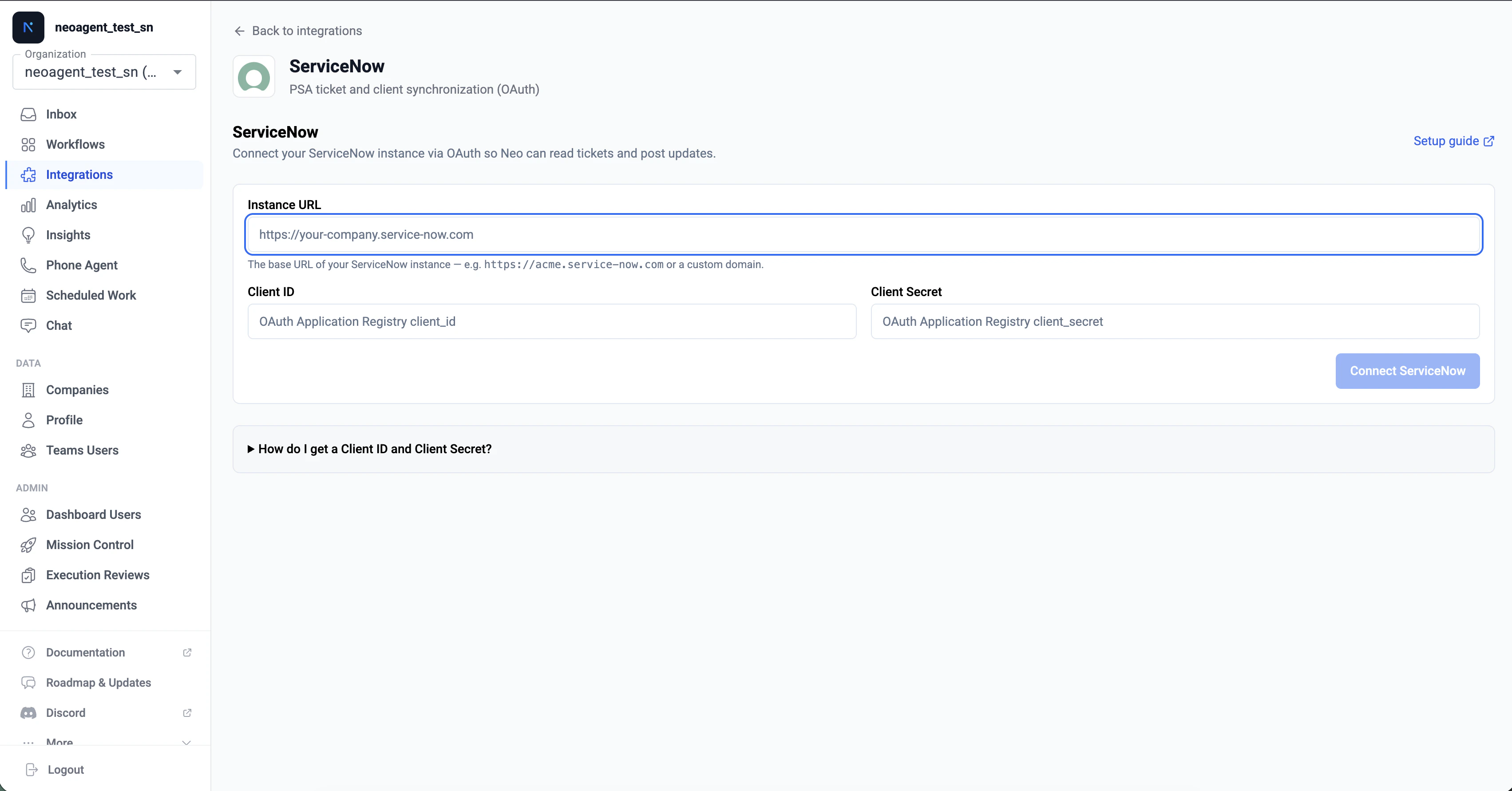
Enter your credentials
Fill in the three fields with the values you collected when creating the OAuth application: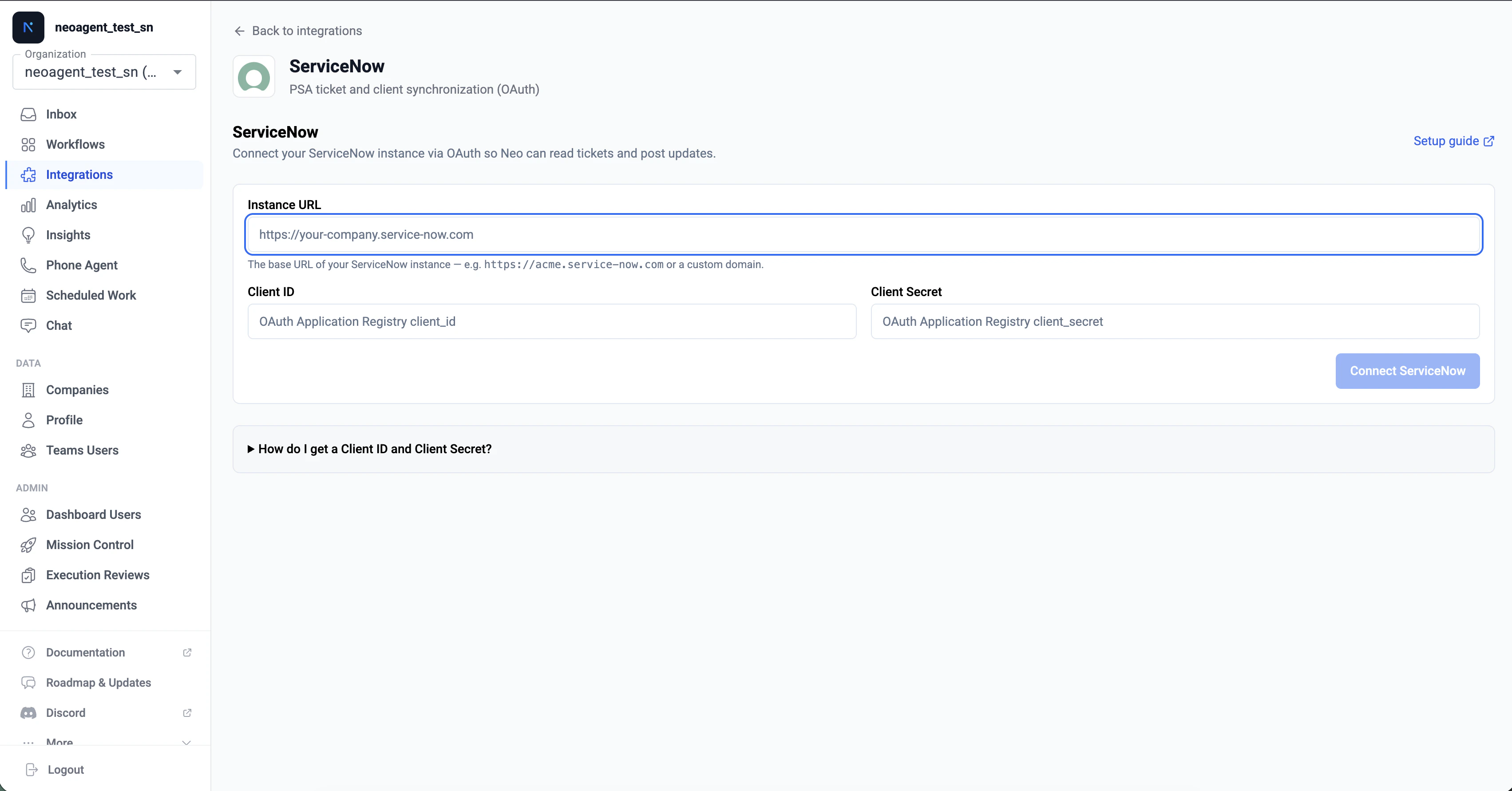
- Instance URL: e.g.
https://acme.service-now.com - Client ID: the Client ID from your OAuth Application Registry entry
- Client Secret: the Client Secret from the same entry
Approve in ServiceNow — sign in as the Neo service account
The popup loads your ServiceNow instance and prompts a user to approve Neo Agent’s access.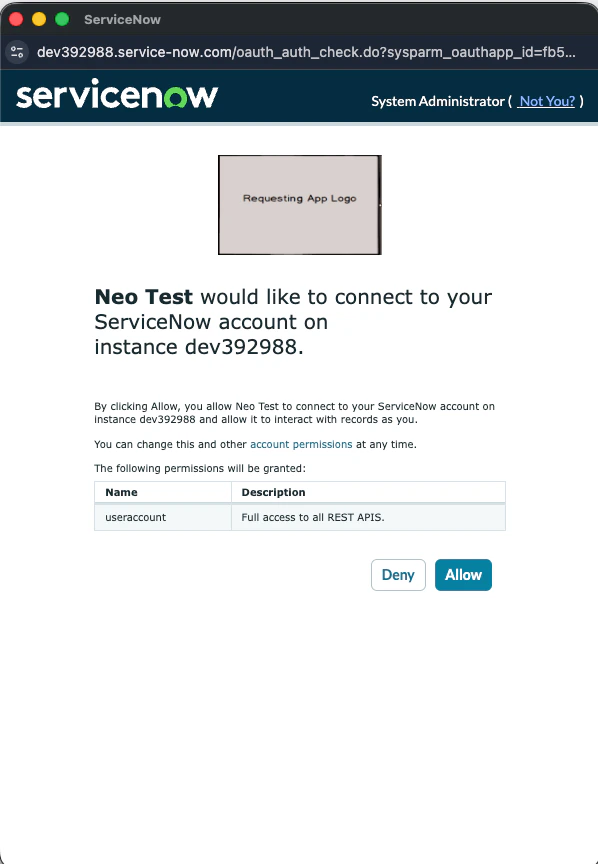
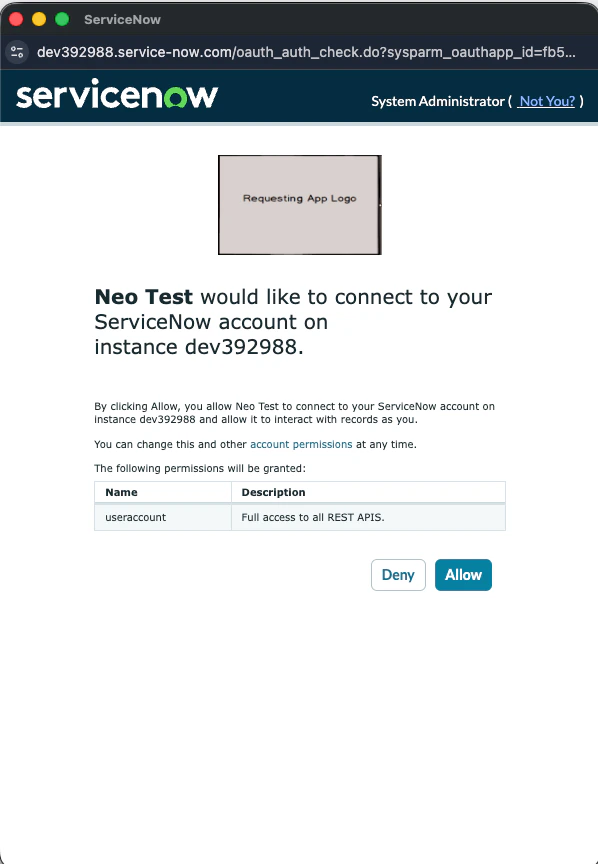
Neo Agent user, or whatever you named it on the previous step). If a different user is signed in, log out of ServiceNow first, then sign in as the service account, then click Allow.The popup closes automatically when consent completes and the dashboard updates to show the integration as connected.Behind the scenes, Neo automatically reads the OAuth user’s
sys_id after consent and stores it as Neo’s identity for ticket assignment and write attribution. You don’t need to enter it anywhere — it’s resolved from the OAuth grant itself. To change Neo’s identity later, log out of ServiceNow, sign back in as the new user, and click Reconnect in the Neo dashboard.Verify the connection
Back in the Neo dashboard, you should see a green ServiceNow connected banner with your instance URL displayed.Behind the scenes, Neo automatically:
- Validated the OAuth refresh token by fetching an access token
- Provisioned a Business Rule on the parent
tasktable in your ServiceNow instance (named Neo Agent — Task Webhook) — fires on every task-family subclass via SN’s table inheritance - Created a System Property (
x_neoagent.callback_url) holding the per-tenant callback URL the Business Rule POSTs to - Set the integration’s sync state to READY_TO_SYNC
A successful connection means Neo has both API access (for reads and writes) and webhook delivery (for real-time event notifications). No further ServiceNow-side configuration is required.
Troubleshooting Connection Issues
If you encounter issues during the connect flow, check the following:`instance_url must be a service-now.com or servicenowservices.com domain`
`instance_url must be a service-now.com or servicenowservices.com domain`
- Make sure the URL starts with
https://(nothttp://) - The hostname must end with
.service-now.comor.servicenowservices.com(FedRAMP/GovCloud customers) - Don’t include a path — just the bare host.
https://acme.service-now.comis correct,https://acme.service-now.com/nowis not - Vanity URLs are not supported here. Use the canonical platform admin URL even if your end users access ServiceNow via a custom hostname
`OAuth callback failed: invalid_client`
`OAuth callback failed: invalid_client`
- Verify the Client ID matches the OAuth Application Registry entry exactly — copy-paste, don’t retype
- Check the Client Secret was copied correctly without extra spaces or newline characters
- Confirm the OAuth application is set to Active in ServiceNow
- If you regenerated the Client Secret in ServiceNow, update it in Neo via the Reconnect button
Popup opens but immediately closes with no consent screen
Popup opens but immediately closes with no consent screen
- The Redirect URL on your OAuth Application Registry entry probably doesn’t match. Verify it’s exactly:
https://dashboard.neoagent.io/oauth/servicenow/callback - Extra trailing slashes, query parameters, or
http://(instead ofhttps://) will cause this. The match must be byte-for-byte
`Insufficient privileges` after OAuth completes
`Insufficient privileges` after OAuth completes
- The user that approved consent doesn’t have the
itilrole — Neo can authenticate but can’t read tickets - In ServiceNow, navigate to the user record and assign the
itilrole (or your equivalent role with Table API read/write on thetaskfamily) - Click Reconnect in the Neo dashboard to retry — the new permissions take effect on the next refresh
`403` errors when Neo tries to send an email via PSA
`403` errors when Neo tries to send an email via PSA
- Neo’s “Email (sent via PSA)” notification mode hits
/api/now/v1/email, which requires theemail_api_sendrole on the integration user (separate fromitil) - In ServiceNow, navigate to the user record and assign the
email_api_sendrole - No reconnect needed — the next workflow run will pick it up. Neo will also raise an inbox alert with this exact remediation when it sees the 403
Connected but webhooks aren't arriving
Connected but webhooks aren't arriving
- Check System Definition → Business Rules in ServiceNow for a rule named Neo Agent — Task Webhook on the
tasktable. It should exist and be Active - Verify System Definition → System Properties contains
x_neoagent.callback_urlpointing at ahttps://...neoagent.io/callback/servicenow?...URL - If either is missing, click Reconnect in the Neo dashboard. The webhook provisioning step is idempotent — it’s safe to re-run, and re-running fixes most provisioning failures (including removing the legacy
Neo Agent — Incident Webhookrule on instances connected before mid-May 2026) - See Webhook Architecture for the full provisioning flow
Network connectivity
Network connectivity
- Confirm your ServiceNow instance is reachable from the public internet over HTTPS
- If you have IP allowlisting enabled in ServiceNow, whitelist Neo Agent’s IP address
- The OAuth round-trip happens in the user’s browser, but the ongoing API calls and webhook deliveries flow between Neo’s backend and your ServiceNow instance directly
What’s Next?
Once connected, every task-family record on your ServiceNow instance — incidents, requests, request items, tasks, change requests, and problems — will start flowing through Neo’s event pipeline. From here you can:- Build workflows — create automated workflows that triage, route, comment, and resolve ServiceNow tickets. Use the Ticket Type filter in the rules-builder to scope a workflow to specific subclasses (e.g., “fire on incidents and changes only”)
- Configure permissions — fine-tune which areas Neo can read versus write in the Neo dashboard’s permission groups
- Train your team — introduce your technicians to Neo Agent’s capabilities and how to work with it
- Monitor performance — track Neo’s impact on ticket resolution times and technician productivity
Your ServiceNow integration is now connected. Real-time webhook deliveries and API operations are both active.
